Commonality and distinctions of Cybersecurity Assurance Level and Risk Value in ISO/SAE 21434
Posted: December 5, 2023
ISO/SAE 21434 had its first edition released in 2021. There are two concepts related to threats initiated in ISO/SAE 21434:
CAL (Cybersecurity Assurance Level) and RV (Risk Value).
Definition and Requirements of CAL and RV
Cybersecurity Assurance Level (CAL) is referred to three times in the context of ISO/SAE 21434:
[RQ-09-05] Cybersecurity goal – NOTE 4 as:
if applicable, a CAL can be determined for cybersecurity goals.
If the countermeasure or requirement for a threat is necessary mitigation, then a cybersecurity goal shall be derived, and a CAL should be defined as an attribute of it as well.
The other two references are in the product development lifecycle and cybersecurity validation [RQ-11-01] NOTE 3:
- CAL can be used to scale the depth and rigor of the activities in this clause and the methods used for them (see Table E) and,
- CAL can be used to scale the depth and rigor of the penetration testing (see Table E).
While not mandated by the standard, it is essential to define the CAL for each cybersecurity goal in practice. This is particularly important for guiding the rigor of development activities and selecting methodologies throughout the entire vehicle development lifecycle.
Risk Value (RV) is referenced several times in the standard context, which can be summarized as:

RV assesses and quantifies the risk levels of threat scenarios by considering impact rating and attack feasibility. Possible evaluation methods include metrics or formulas, proposing risk value ranges from 1 to 5, where 1 indicates minimal risk and 5 represents maximal risk. Different risk values necessitate corresponding countermeasures and follow-up activities.
If the risk value is assessed as very high, which is undesirable during the design phase, redesigning may be the only solution to eliminate the risk. Should risk treatment involve reduction, a cybersecurity goal must be established to mitigate the risk to an acceptable level. Alternatively, a cybersecurity claim can be made to justify risk sharing or retention. Risks assessed as very low, specifically RV = 1, can be omitted. This assessment is equivalent to accepting the risk with no need for further analysis or development activities.
Assessment of CAL and RV
The assessment of CAL and RV is proposed in tables E and H of ISO/SAE 21434 as below:
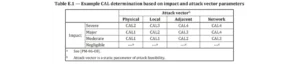
CAL is defined as CAL 1/2/3/4 which corresponds to an assurance level low to moderate/moderate/moderate to high/high, it evaluates the impact and attack vector, and the general principle is that the assurance level should be proportional to the impact severity and potential attack distance.
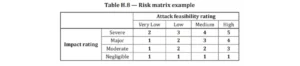
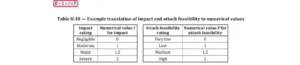
RV is ranged as [1…5] corresponding to risk level from low to high, which can be evaluated by metric or formula, both methods output the same assessment results for the threat scenario.
Both CAL and RV assessments consider the impact of threats as one dimension. However, they differ in another dimension: RV includes the feasibility of an attack as a key factor, which can be evaluated using various methods such as Attack Potential, CVSS, or Attack Vector, as recommended in the standard. In contrast, CAL solely focuses on the Attack Vector, one of the three methods for assessing attack feasibility. The Attack Vector method, with its limited scope (considering only physical distance for attack detection), offers the least comprehensive evaluation. By comparison, the Attack Potential method accounts for more factors, including the time and equipment needed for an attack, professional knowledge and technology, understanding of the system or its components, and the window of opportunity.
Based on the differences in the evaluation dimensions, the standard gives the relationship between CAL and RV in the whole vehicle lifecycle:
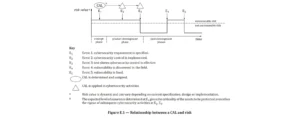
CAL can be determined during the conceptual phase and remains static throughout all subsequent phases of product development since the physical distance to achieve an attack does not vary in different phases of the vehicle lifecycle and technologies.
Risk Value (RV) can be effectively decreased through analysis and quantification in the conceptual phase. This process is followed by the design and implementation of corresponding control strategies during the development phase. Subsequently, these controls are validated to ensure their effectiveness in reducing the risks to an acceptable level of reasonableness. Once vulnerabilities in systems are identified, or when new technologies render these systems more susceptible to attack, the RV will increase to reflect the changes in the risk situation. It will then decrease again once mitigations are deployed and confirmed effective. In contrast to the constant nature of the CAL, the RV may vary dynamically throughout the entire vehicle lifecycle. This includes phases such as maintenance and decommissioning, changing over time.
In terms of evaluation factors between CAL and RV, RV has a more comprehensive and targeted assessment of risks, yet its dynamic characteristics cannot ensure certainty and consistency throughout all stages of the vehicle lifecycle. Therefore, the CAL, characterized by its static evaluation dimension, serves as an attribute for cybersecurity goals and requirements. It specifies the rigor required in subsequent development stages and dictates the methodologies to be adopted.
CAL influence on vehicle development
There are some proposals on how CAL should guide the development activities and processes in the standard (Annex. E):
- Selection of development and verification methods
- Selection of vulnerability identification and analysis methods
- Selection of Cybersecurity Assessment Methods
The recommended independence of cybersecurity engineering in the standard:

For the verification of cybersecurity design, implementation, and integration, as well as for cybersecurity validation, different levels of independence are recommended based on the Compliance Assurance Level (CAL). CAL1 and CAL2 suggest an independence level of 1, which requires the involvement of a different person. In contrast, CAL3 and CAL4 recommend an independence level of 2, necessitating the involvement of a person from a different team.
Furthermore, if the situation falls under CAL4 for cybersecurity assessment, it demands an even higher degree of independence. This entails the involvement of a person from a different management structure and with distinct resources. The overarching requirement for development activities is to maintain a rigor that corresponds with the higher independence level. Notably, the definition of independence level in this context is quite comparable to that in ISO 26262.

Different CALs dictate distinct testing methods or varying levels of rigor for the same method. For instance, penetration testing is mandatory only for CAL3 and CAL4, while it’s not required for CAL1 and CAL2. In contrast, requirements-based testing for functional testing suffices for CAL1 and CAL2. However, for CAL3 and CAL4, additional testing of interfaces and interactions is necessary.
The examples above illustrate how ISO/SAE 21434 provides guidelines on utilizing CAL to enhance the development process. These guidelines can serve as a reference point for all activities and processes in vehicle cybersecurity engineering. In practice, organizations can tailor these principles to fit their specific situations and constraints, ensuring the security of their vehicles.
It is important to note that the organizations should communicate their strategy with the supply chain upstream and downstream to reach alignment in the specific project, so as not to lead to inconsistent criteria for project development activities.
In summary, in the realm of vehicle cybersecurity engineering, CAL and RV each have distinct roles. CAL, as an attribute of cybersecurity goals and requirements, specifies the rigor of development activities and processes. It facilitates a common understanding throughout the entire supply chain, with a higher CAL demanding more effort and resources. Meanwhile, RV is determined by analyzing the impact and likelihood of attacks to gauge the severity of threats. This analysis informs decisions about the necessity and nature of cybersecurity controls, even in the post-development phase, to effectively mitigate risks.
SystemWeaver Cybersecurity Solution
SystemWeaver’s cybersecurity solution offers a comprehensive approach to managing cyber risks. It includes defining and analyzing both CAL and RV. Additionally, it assesses the effectiveness of cybersecurity controls by demonstrating how risk assessment and implemented countermeasures can reduce risks both before and after the cybersecurity engineering process.

The cybersecurity goals and the derived requirements will automatically inherit the Cyber Assurance Level (CAL) assigned to each identified threat. This assignment guides the subsequent development activities to address these threats effectively.

If there is more you would like to explore about SystemWeaver, you are welcome to reach us at info(at)systemweaver.com!


